You can read our current Counter Terrorism Policy here: Counter Terrorism Policy
Other Useful Resource Links:
www.assets.publishing.service.gov.uk/government/CT_Awareness_-_Helpful_Advice_Leaflet.pdf
www.gov.uk/government/publications/stay-safe-film
If you’ve seen or heard something that could potentially be related to terrorism, trust your instincts and report it. Your actions could save lives.We at Leisuresec understand that the threat from terrorism is serious. The main threats to national security are terrorism, espionage, cyber threats and the proliferation of weapons of mass destruction, many of which impact on the UK’s national infrastructure.
You can now Report Online any suspicions in confidence via ACT and the Metropolitan Police.
The threat to the UK (England, Wales, Scotland and Northern Ireland) from terrorism is:
SUBSTANTIAL

The current UK threat level for terrorism can be located on the gov.uk website’ https://www.gov.uk/terrorism-national-emergency


The National Counter Terrorism Security Office (NaCTSO) has refreshed their 'Crowded Places Guidance' to help people respond safely to incidents involving hazardous substances – prompting people to act quickly, which can save lives.
The 'REMOVE, REMOVE, REMOVE' procedure has now been added to the Chemical, Biological and Radiological (CBR) Attacks section and is designed to support first responders.
READ MORE:
- National Counter Terrorism Security Office (NaCTSO)
- Crowded Places Guidance
- Acid Attacks NHS guidance
ACT | ACTION COUNTERS TERRORISM
Communities defeat terrorism. With the enduring terrorist threat, it is now more important than ever that everyone plays their part in tackling terrorism. Your actions could save lives.
That’s why we are supporting the Action Counters Terrorism (ACT) initiative. It is encouraging communities across the country to help the police tackle terrorism and save lives by reporting suspicious behaviour and activity.
Like other criminals, terrorists need to plan. If you see or hear something unusual or suspicious trust your instincts and ACT by reporting it in confidence at gov.uk/ACT an emergency, dial 999.
Read more about ACT - https://act.campaign.gov.uk/
Some examples of suspicious activity or behaviour could potentially include:
- Hiring large vehicles or similar for no obvious reasons
- Buying or storing a large amount of chemicals, fertilisers or gas cylinders for no obvious reasons
- Taking notes or photos of security arrangements, or inspecting CCTV cameras in an unusual way
- Looking at extremist material, including on the so-called Dark Web, or sharing and creating content that promotes or glorifies terrorism.
- Someone receiving deliveries for unusual items bought online.
- Embracing or actively promoting hateful ideas or an extremist ideology.
- Possessing firearms or other weapons or showing an interest in obtaining them
- Holding passports or other documents in different names, for no obvious reasons
- Anyone who goes away travelling for long periods of time but is vague about where
- Someone carrying out suspicious or unusual bank transactions
Any piece of information could be important, it is better to be safe and report. Remember, trust your instincts and ACT. Action Counters Terrorism.
Useful for New Starters to view the video as part of the induction plan + add to training record + increase ACS score
https://www.gov.uk/government/news/travel-industry-training-staff-to-deal-with-terrorist- incidents

Recognising Terrorist Threats
Terrorists can choose from a broad range of potential methodologies that may be used when they carry out an attack. These can vary from small scale attacks, where a bladed weapon is used to undertake a localised attack, to large scale atrocities where truck bombs have been used to cause mass devastation, or layered attacks, where a combination of attack methodologies are used to cause maximum disruption.
ALL attacks have indicators, either that they are about to occur or have just started. In studying these, NPSA research has found that quick recognition that an attack is occurring, partnered with a timely response can reduce casualty numbers and save lives. To facilitate this, it is essential that security staff have improved awareness in key indicator recognition.
NPSA, in collaboration with ACT, have published the Recognising Terrorist Threats guide aimed at every level of the security profession. Drawing on NPSAs extensive research programme and post event analysis, the guide contains an overview of potential terrorist methodologies, key components of threat devices and other potential attack indicators.
You can download the guide here.
In the role of a security operative you are most likely to encounter a direct phone call to the business premise or the discovery of a suspicious package.
If a suspicious package is discovered the first step is to safeguard people so they must be advised to stay well clear without causing panic or alarm. In no circumstances should the person discovering a suspicious package or object attempt to remove it.
Do not touch it or try to look inside. Isolate the area. Keep all persons well away from it. Try to establish if the package belongs to anyone in the vicinity.
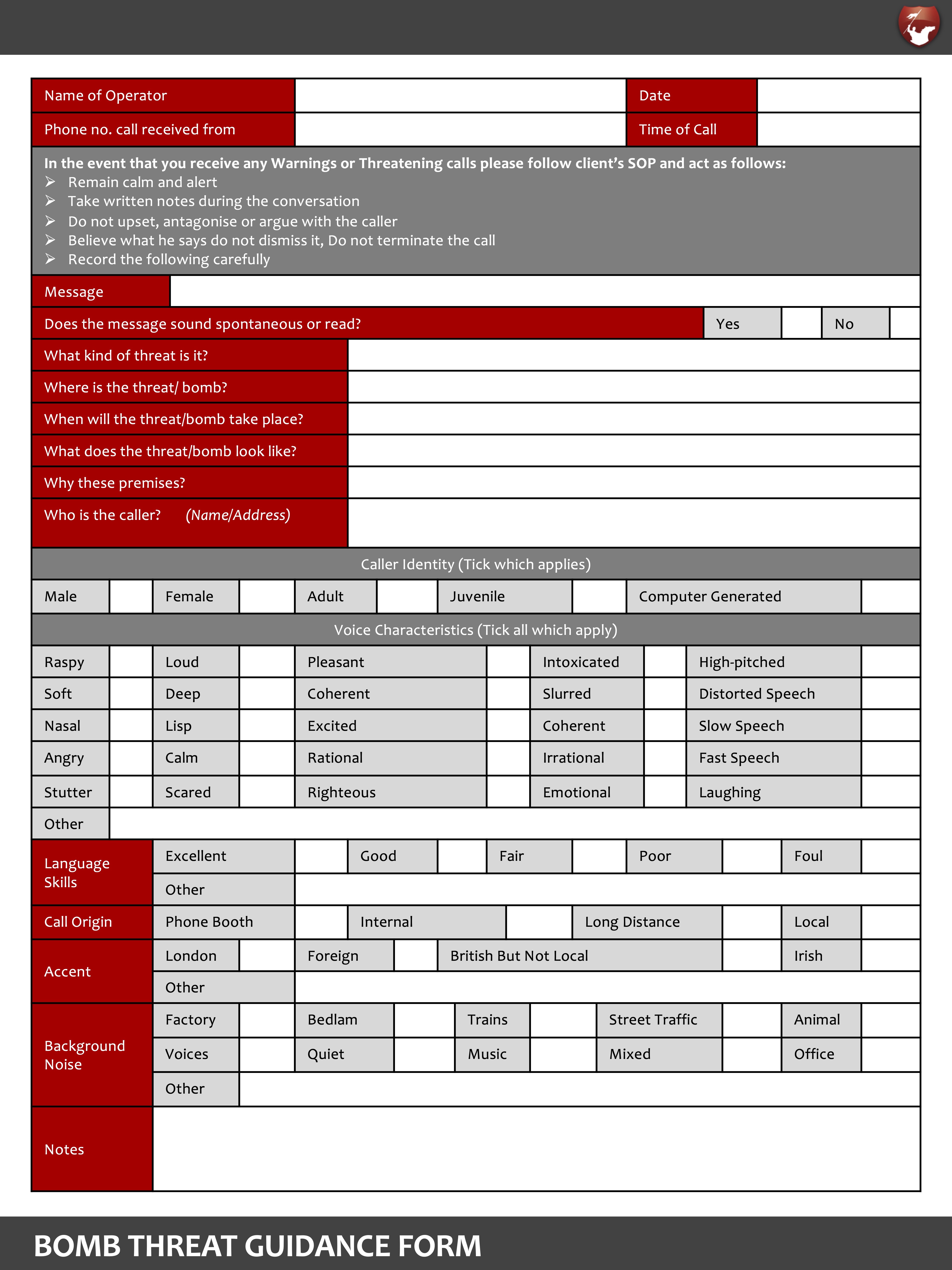
On receipt of a telephone bomb threat, the person who took the call should complete the Bomb Threat Check Sheet and follow these procedures:
Remember: suspect bombs should only be dealt with by explosives experts.
The current UK threat level for terrorism can be located on the gov.uk website’ www.gov.uk/terrorism-national-emergency
National Counter Terrorism Security Office (NaCTSO) trials new ProtectUK website
ProtectUK is now available. ProtectUK is the new counter-terrorism platform with accessible up-to-date guidance. The primary audiences for ProtectUK are you, our approved contractors, and licence holders.
The ProtectUK website is free and it is supported by the ProtectUK app which is available from any device.
The ProtectUK app provides guidance on:
• Practical advice and guidance to help you protect your business, plus information on how to respond in the event of an attack
• Information on CT Policing’s suite of ACT training products, plus access to the award winning ACT Awareness e-Learning package
• Access to a suite of NaCTSO guidance videos
• Latest bulletins and information
• Details of the ACT online reporting form and confidential hotline
• Emergency response and post-incident guidance
You can access the ProtectUK app, which is available from the Google Play store and Apple Store on your smart phone.
CPNI's short films to reduce the vulnerability of the national infrastructure to terrorism and other threats
CPNI have produced a short film which introduces the quick actions a member of staff within a small business can take to lockdown their premise during a terrorist incident. The principles of which can be applied across many types of locations and ultimately acting fast can save lives. Additional guidance, can be found on the CPNI website
Suspicious Behaviour
By understanding when suspicious behaviour, such as hostile reconnaissance, can occur and how individuals undertaking it may feel, you have an early indication of potential attack planning and the opportunity to disrupt attacks.
Prior to an attack, it may be necessary for individuals to undertake final preparations such as readying a weapon or priming a device. This behaviour may appear suspicious or out of the ordinary
for your location. The W•H•A•T protocol should be considered when evaluating suspicious behaviour.
What are they doing
How are they behaving?
Alone or acting with others?
Threat- what type do they pose?
What- are they doing?
Are they being violent, or are they just doing something that seems out of place?
Are they attempting to hide/conceal something?
Are they following someone?
Are they taking an unusual interest in security arrangements? (E.g. trying to seekey codes).
How are they behaving?
Do they seem calm, or are they agitated?
Are they trying to avoid detection?
Could they be under the influence of alcohol or drugs?
Are they being confrontational?
Alone or part of a group?
Are they with other people?
If so, do they seem to be acting with a common purpose? (E.g. all moving together).
Have they been with other people who have now moved away?
Do they appear to be pretending not to be with other people?
Threat-what type do they pose?
Are they carrying an obvious weapon?
Do they appear to be concealing a weapon?
Are they carrying a bag or other container? (E.g. a package or a bottle)Are they holding something that could be used as a weapon).


